
Database Security: How It Protects Your Data and Works Hand-in-Hand with Data Encryption
Data is now more valuable than it ever was. Millions of people share and store online information on a daily basis. This may be personal information, business data, or even financial records. Now have you ever thought of how such data are protected? The answer is database security.
Database security is an important element of data protection. Without database security, there is a high risk of data theft, as hackers could easily access classified data. Not only data theft, but it can also lead to more crimes like identity theft, financial fraud, ransomware, and more. In this blog, we will discuss the importance of database security and how it helps with data encryption.
Why Database Security Matters
A database consists of a huge amount of sensitive information. This stored data is the primary target of the cybercriminals. Let’s understand it with an example of a bank. A bank contains all information of their customer, like name, address, and financial data. Now it’s the responsibility of the bank to protect customer data. If their database is not secured properly, the information can be breached, accessed, altered, or even stolen, and what not.
There is also a catch in database protection. Most people think that the database is secured to keep it safe only from unauthorized users. But this is not true at all. Not only unauthorized users, but it’s also important to protect data from inside the database, making sure it remains unharmed.
Protecting Sensitive Information
Databases carry sensitive information like names, addresses, mobile phone numbers, and financial information. These details need to be heavily protected so that they don’t get accessed by unauthorized individuals.
Ensuring Data Integrity
Maintaining data integrity is crucial, as in case the database is not secured, the data can be corrupted, deleted, or changed, which can cause immeasurable damage. Therefore, the data security of the database should allow only authorized users to view, edit, or delete the data.
How Database Security Protects Data Encryption
Data encryption is a great way to protect sensitive information. It consists of turning the readable data into an unreadable format. This process makes sure that even if the data gets accessed, one cannot interpret it without the decryption key.
How Encryption Works with Database Security
Before the data is stored in the database, it is firstly encrypted. As discussed earlier, the encryption converts the original data into ciphertext. Then this first needs to be decrypted by the user to access the data.
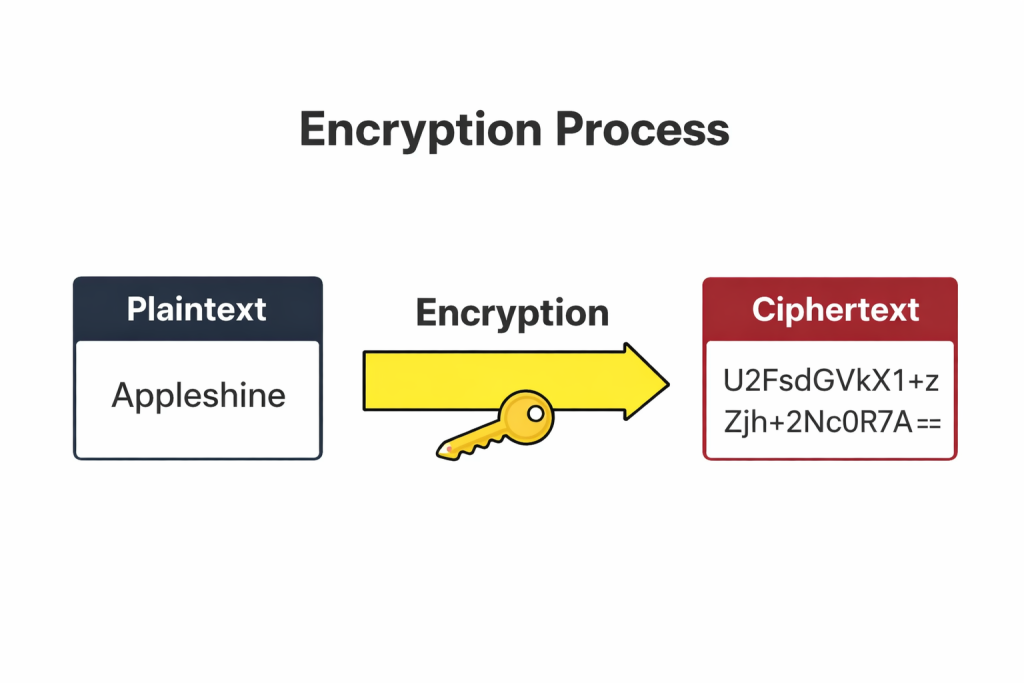
In the above example, “Appleshine Tech” is the plain text, which is then converted to the ciphertext. But what if the encryption key gets stolen? Then the unauthorized user can decrypt the ciphertext and access the data. Thus, it’s important to have database security where the encryption keys are securely stored.
Encryption Keys and Database Security
Management of encryption keys is important for database security. Encryption keys should be well managed to ensure the data security of the entire database. Moreover, you can use hardware-based solutions like ApplshineTech HSM to store the encryption keys to specific hardware modules, where the keys remain safe and secure.
Key Features of Strong Database Security
A well-protected database usually consists of multiple layers of data security. Here are some features that they include:
1. Access Control
It is made sure that only authorized users are able to access the database. Setting up strong access control forbids unauthorized users from logging in and viewing the data. Access control consists of multi-factor authentication, role-based access, and password policies.
2. Encryption
Encryption keys make sure that data is protected and that it is difficult for hackers to decrypt the data stored in the database.
3. Regular Audits and Monitoring
Monitoring and auditing the actions of users who have access to the database can help in identifying doubtful activities and reduce the risk of data breach before it happens.
4. Backup and Recovery
It is always recommended to have a backup of the database. No one knows what can happen; even with the best database security, accidents can happen. That’s why you should make sure to regularly take a backup of your database to avoid losing the data.
Why Database Security and Data Encryption Go Hand-in-Hand
Database security is a vast concept, and encryption is just a small part of it. There should be proper database security; without it, the encryption process is nothing. Hackers can easily break into the database, steal the encryption keys, and decrypt the data. The same goes for the encryption keys; if they are not encrypting the data effectively, the database security alone is not enough.
The combination of both database security and data encryption is a solid defense system for data security. Encryption will protect the data, and the database will protect the keys. These two coming together enables one to create multiple layers of data protection.
How AppleshineTech Can Help Protect Your Data
At AppleshineTech, we know how important it is for you to safeguard your data. Our Hardware Security Modules (HSMs) and database encryption solutions are specifically aimed at protecting data by safely storing encryption keys that can only be accessed by authorized users of the database. If you want to manage your valuable data, you can use our HSMs that provide the best data security.
Conclusion
As data is now growing day by day, it’s also important to protect data. Using database security will make certain that your data is secured and that data integrity is in check. In the current scenario, the number of cyberattacks is increasing, so make sure to adopt a powerful security system to prevent the risk of data breach.
Always consider using trusted database security solutions like AppleshineTech’s HSMs to keep your encryption keys stored carefully and protect your sensitive data.
FAQs
1. What is database security?
Database security refers to the use of multiple pillars of protection that protect your data from unauthorized and malicious activities.
2. How does data encryption protect my data?
Data encryption converts plaintext (data) into ciphertext, which makes it difficult to understand without the use of a decryption key.
3. Why is managing encryption keys important?
Encryption keys are the source through which the encrypted data is decrypted. Thus, mismanagement of encryption keys can lead to data breaches.
4. How can HSMs help secure my data?
HSM stores the encryption keys in a tamper-resistant structure that prevents unauthorized access of data.
5. What should I look for in a database security solution?
Look for a database security solution that has strong encryption, access control, a monitoring system, and a backup and recovery model.

