
Software Security Development Lifecycle (SSDLC): What It Is, Key Phases and Best Practices
The Software Security Development Lifecycle (SSDLC) is an infrastructure that integrates security steps at every stage when building software. Software developers should follow these steps from the beginning of the development stage to keep the software safe.
While in the traditional Software Development Lifecycle (SDLC) there was a big problem. The security was added after the software was fully made, which makes the process both expensive and time-consuming.
Thus, SSDLC encouraged the big companies to find out ways in which they can make their software secure before starting to create it.
Benefits of Implementing SSDLC
- Lowers cost by focusing on security from the start.
- Reduces the risk of vulnerability in the software.
- Helps to comply with security standards like PCI DSS and GDPR.
- Identification of flaws in software security.
- Quick response to threats by regular monitoring and checks.
Key Principles of SSDLC
The software security development lifecycle follows these core principles:
1. Shift Left
Security checks should be implemented before the development stage. The earlier the problem is identified, the easier and cheaper it will be to fix.
2. Risk-Based Approach
The developer teams must focus on identifying areas that are vulnerable and are likely to get attacked or exploited.
3. Defense in Depth
By adding multiple layers of security, developers can protect their software even if one of the security layers gets breached.
4. Continuous Improvement
Security threats are evolving and coming in different ways. Therefore, the developers are required to learn and stay relevant to the latest security practices.
5. Compliance and Standards
Developers must follow security standards like PCI DSS, ISO or OWASP. These standards make sure that the software adheres to the security requirements.
The 5 Phases of SSDLC
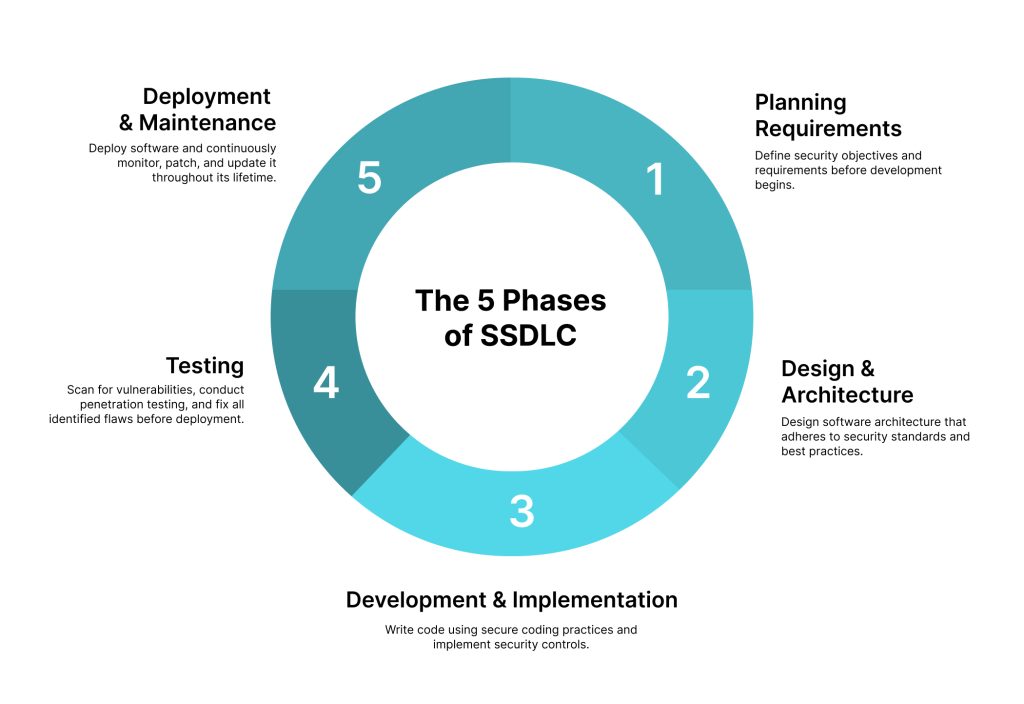
1. Planning Requirements
Planning is the most important phase in the software security development lifecycle. A systematic plan should be created before the developers start to code. The plan must define the security requirements that need to be fulfilled. Accordingly, the developers and architects will work together to remove any vulnerability in the software.
2. Design & Architecture
In the second phase, the team starts to design the software. The software should be designed as per the plan that was previously created. Additionally, the team should look into the security architecture to make sure that their software adheres to the latest security standards.
3. Development & Implementation
At this stage the actual coding of software begins. Along with coding, developers also follow secure coding practices to avoid security threats like SQL injections and XSS. These codes are then implemented into the codebase, where they will be further reviewed by the team.
4. Testing
After the development is done, developers can start testing the security controls. This can be done by scanning, penetration testing and using code analysis tools to find potential flaws. A detailed report must be created if any weak spot is found and must be fixed before deployment.
5. Deployment & Maintenance
This is the final phase where the software is deployed. The developer’s job doesn’t end here. Regular monitoring of the software should be done to look for any security issues. Security updates and patches should be created for any discovered vulnerability. Moreover, using HSM or key management solutions can also help keep the software safe.
SSDLC Best Practices
- Use automated tools to quickly scan the code and find any flaws that need to be fixed.
- Developers may regularly review codes to prevent any issues in software.
- Provide limited access to users.
- Update to the latest security tools.
- Maintain clear documentation of security audits.
Common SSDLC Frameworks
Microsoft Security Development Lifecycle (MS-SDL)
The Microsoft Security Development Lifecycle is one of the most widely used frameworks by the software developers. It includes:
- Threat modeling
- Security training
- Incident response Planning
NIST Secure Software Development Framework (SSDF)
The NIST framework provides certain guidelines for a secure software development process. It majorly focuses on 4 key areas:
- Preparing the organization
- Protecting the software
- Producing secured software
- Responding to vulnerabilities
OWASP Software Assurance Maturity Model (SAMM)
OWASP SAMM helps companies analyze their current security practices and improve them. It covers 5 business functions:
- Governance
- Desgin
- Implementation
- Verification
- Operations
Strengthen Your SSDLC with the Right Security Tools
A solid SSDLC framework may remain incomplete without the right tools. It is important that security must be added at every layer of your software.
At AppleshineTech, we provide strong cyber security solutions like HSM modules and Key Management solutions that are designed to support the entire software security development lifecycle and safeguard your software.
Why Choose AppleshineTech:
- Trusted Thales implementation partner.
- Over 10+ years of experience in IT security.
- Complies with security standards like PCI DSS, ISO and GDPR.
By integrating SSDLC with our reliable cyber security solutions, you can easily protect your software from security threats.
Get your cyber security solution at AppleshineTech today!
Conclusion
In conclusion, the Software Security Development Lifecycle is an important aspect in software development. With the increasing cyberattacks, having a proper SSDL is a must for organizations.
By integrating the best SSDLC practices, businesses can protect their software from getting harmed. Additionally, using cyber security solutions like HSM and Key Management Solutions can safely secure sensitive information throughout the software development lifecycle.
Frequently Asked Questions (FAQs)
Q1. What is the difference between SDLC and SSDLC?
SDLC (Software Development Lifecycle) is the process of building software, whereas SSDLC (Software Security Development Lifecycle) adds security steps at every phase of the SDLC.
Q2. Why is SSDLC important for businesses?
SSDLC is important for businesses because it helps make the software safe, reduces security risks, minimizes cost and stays compliant with security standards.
Q3. What are the five phases of SSDLC?
The five phases of SSDLC include planning requirements, designing, development, testing and deployment. These steps help build the software while maintaining
Q4. Which SSDLC framework should I start with?
If you are just starting the SSDLC process, consider OWASP SAMM framework as it helps analyze the current security and improve it step-by-step. For more developed organizations, using NIST SSDF or MS-SDL will be an ideal choice.
Also Read:
Understanding the DPDP Act: Key Provisions and Its Impact on Data Protection Compliance
Top Cybersecurity Tools Every Company Should Use

