
Payment HSM: Why It Is Essential for Secure Digital Transactions in 2026
In 2026, the world is shifting towards digital means of payment. People are now using UPI, debit cards, or net banking for any payment transaction. These digitalized transaction methods have become the most convenient way to perform smooth and fast transactions. But behind these transactions, there is a strong security system often referred to as a Payment HSM. These systems work silently to protect the transactions from cybercrimes.
In this blog, you will learn all about Payment HSM, what it does, how it works, and why it is important for maintaining safe digital transactions.
What Is a Payment HSM?
Payment HSM is a hardware device that is required to secure your transactional data. Its main purpose is to protect payment-related information like card numbers, PINs, transaction details, and encryption keys.
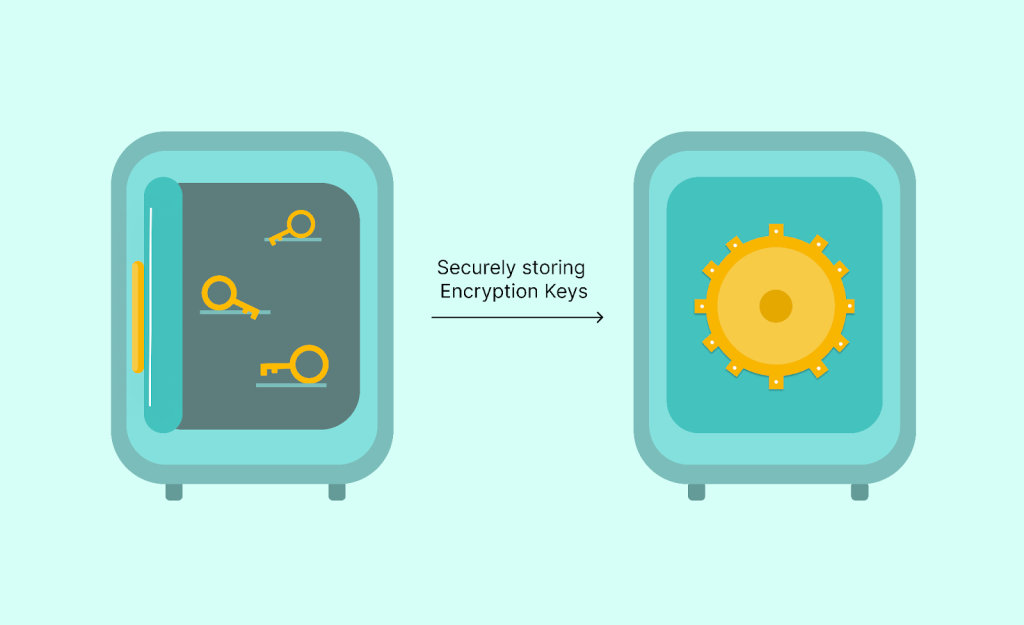
Let us help you to understand it clearly by taking an example of a locker. The purpose of a locker is to store valuables to keep them safe. Similarly, here the Payment HSM is the locker, and the encryption keys are the valuables that are stored inside it.
What Does a Payment HSM Do?
A Payment HSM performs the following tasks:
- Encryption keys generation
- PIN verification
- Encrypting and decrypting card data
- Protecting ATM and POS transactions
- Supporting payment compliance standards
These things make sure that the data remains protected and safe.
Types of HSM Modules Used in Payments
1. On-Premise HSM Modules
They are HSM devices that are placed within a company’s data center. Such types of modules are mostly used by banks.
2. Cloud HSM Modules
These modules are cloud-based, which helps businesses to store their encryption keys safely. Users can easily access information remotely.
3. Network HSM Modules
These HSM devices are responsible for managing transactions in large volumes over the payment networks.
Why Payment HSM Is Important in 2026
1. Prevents Payment Fraud
Payment fraud is currently the biggest problem when it comes to online transactions. The absence of strong encryption can result in the exploitation and misuse of payment data by the hackers. Payment HSM can help prevent these frauds by encrypting the data so that it remains unharmed and protected.
2. Protects Encryption Keys
Encryption keys are crucial for data security. In case these keys get stolen or are exposed to any unauthorized person, the data can get breached. In order to keep the encryption keys safe, the Payment HSM provides multiple layers of protection, making it difficult for unauthorized users to access the information.
3. Secures Payment Data in Real-Time
Online transactions are performed by the payor to the payee in real time. Thus, the payment must be encrypted instantly. Payment HSM starts the encryption process from the moment the transaction is made. This protects the data from being exposed during the payment process.
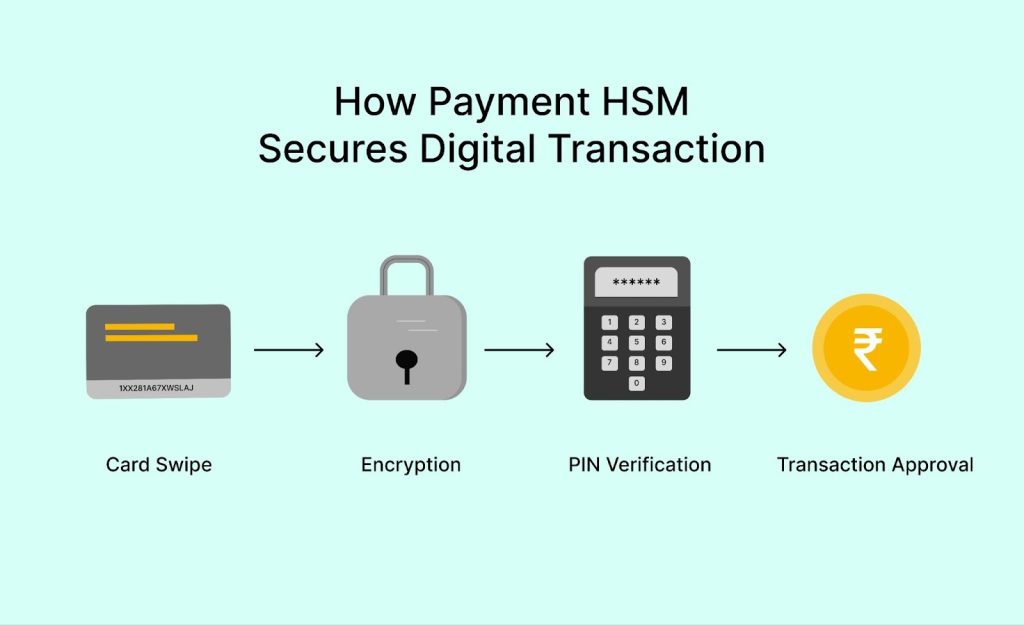
How Payment HSM Secures Digital Transactions
Now let’s see how Payment HSM works during a transaction:
Step 1: Card Swipe or Online Payment
The customer makes a payment through the card or UPI. When the payment action is made, the system automatically captures the data.
Step 2: Encryption Begins
The captured data is encrypted by the HSM system. It involves the conversion of readable data into ciphertext.
Step 3: PIN Verification
The customer’s PIN will be securely verified by the HSM system without exposing it. The Payment HSM ensures that the PIN doesn’t appear in an unencrypted form.
Step 4: Secure Transaction Approval
If the PIN verification is successful, the transaction is approved, and vice versa.
In this entire process, the Payment HSM never leaves out the encryption keys. This keeps the transaction process smooth and secure.
Payment HSM Compliance Requirements
Businesses in 2026 are required to strictly follow the payment security rules. Following are the security standards:
- PCI-DSS (Payment Card Industry Data Security Standard)
- FIPS security certifications
- RBI guidelines for banks in India.
Non-compliance with these rules may lead to:
- Heavy penalties
- Loss of customer trust
- Legal complications
Thus, businesses should always use a certified Payment HSM that meets these security standards.
Why AppleshineTech Is a Trusted Partner for Payment HSM Solutions
At AppleshineTech (Thales Implementations partner), we provide your business the best Thales HSM solution according to its transaction volume and security compliance. Unlike other HSM providers, we first prioritize your security needs and then provide a suitable solution for your business.
Our Payment HSM offers the following services:
- Secure HSM deployment
- Encryption key management
- Payment data protection
- Compliance-ready HSM integration
- Expert consultation and support
Therefore, you don’t have to worry about your business payment security. Our Payment HSM will protect and safeguard your data and prevent it from being exposed or leaked.
Conclusion
Digital payments have become a part of our human life. From buying products online to transferring instant money, we depend on secure systems. By using a strong Payment HSM from top HSM vendors like AppleshineTech, you can protect your encryption keys and PINs while complying with the security standards.
Thus, it’s important for businesses to install a secure Payment HSM so that the transactional operations are performed quickly and securely.
FAQs
1. What is a Payment HSM?
Payment HSM is a hardware device used to protect and secure encryption keys, PINs, and digital payment transactions.
2. Why is Payment HSM important?
Payment HSM is important because it helps avoid data being breached during the transactional process.
3. Is Thales HSM a good option for payments?
Yes, Thales HSM is a good option for payment security. It is a trusted HSM solution used by multiple banks and financial institutions.
4. What are HSM modules?
HSM modules are devices used for safely storing data through cryptographic actions.
Also Read:
Top HSM Vendors in India: A Complete Guide for Businesses 2026
Key Management in Cryptography: The Essential Guide to Securing Your DataDatabase Security: How It Protects Your Data and Works Hand-in-Hand with Data Encryption
The Role of HSMs in Securing Digital Payments and Financial Data
What Is Key Management? A Practical Guide to Securing Encryption Keys

