
Key Management in Cryptography: The Essential Guide to Securing Your Data
Do you know how your personal data is kept safe when you share it over the internet? It’s done through cryptography and the way the encryption keys are managed. This keeps your digital data, like bank details, emails, or private messages, safe from hackers and unauthorized users. In this blog we will explain the concepts of key management in cryptography, its importance, and how it secures your data.
What Is Key Management in Cryptography?
Key management in cryptography refers to the process that needs to be followed for secure management of the encryption keys. These encryption keys are essential for data security, as they convert the readable data into unreadable data known as ciphertext.
In cryptographic systems two types of keys are used:
- Symmetric keys: This is a single key that is used for both encryption and decryption of data.
- Asymmetric keys: It has two different keys. One is used to encrypt the data, and the other is used to decrypt the data.
Thus, the safety of these keys used in cryptography systems should not be compromised. With a proper key management system, data becomes invulnerable to attackers and remains unharmed.
Why Is Key Management Important?
Given below are some reasons regarding the importance of a key management system:
1. Preventing Unauthorized Access
Proper management of encryption keys prevents data from being accessed by unauthorized users. Mismanagement of these keys can cause a data breach in the database.
2. Maintaining Data Confidentiality
It is important that data remain confidential. Securely stored management of keys helps in maintaining this confidentiality and makes it safe from hackers.
3. Ensuring Data Integrity
Data integrity means that data should be accurate and consistent. It is the responsibility of the key management system to ensure that the data remains the same and doesn’t get changed or deleted.
4. Complying with Regulations
Sectors like the financial and medical sectors are required by law to have top-notch security in order to safeguard the data. To meet the regulations of law, these sectors must use a key management solution to handle the data.
How Key Management Works
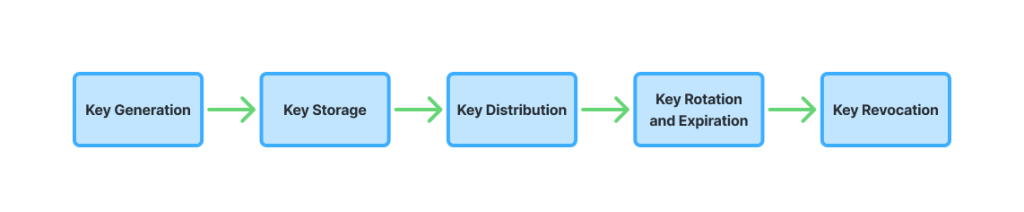
Key management consists of certain steps:
1. Key Generation
The first thing to do is to generate an encryption key. It should be noted that during the creation of the key, the process should be done in a safe place to prevent any unauthorized access. Moreover, keys should be generated randomly to make them unpredictable.
2. Key Storage
After the keys are generated, they now need to be stored securely. Never store keys in plain text, as they can be easily attacked by hackers. Rather, store the keys in the HSM system to maintain security.
3. Key Distribution
Once the keys are stored safely, they need to be distributed to the immediate authorized users and systems to encrypt or decrypt data. This is a crucial step and must be done carefully.
4. Key Rotation and Expiration
The keys should be periodically changed to maintain security. Most key management systems offer automatic key rotation. What it does is that it replaces the old keys with new keys after a period of time. Along with key rotation, the keys should also be set to expire to reduce any further risks.
5. Key Revocation
If a specific key is no longer needed, it should be removed. In simple words, it means removing any invalidating or unused key before its expiration period.
AppleShineTech Key Management Solutions
Instead of manually managing the keys, organizations prefer a key management solution (KMS) to manage the keys. Key management solutions, like AppleshineTech, provide automation of management and security of the keys. Besides that, it also manages the whole lifecycle of the cryptographic keys from their creation to their destruction, providing a reliable infrastructure to manage these keys and keep them safe.
Choosing the Right Key Management System
If you are looking for a key management solution, we have provided you a checklist of things that you should consider before using it:
- Must have strong encryption standard like the Advanced Encryption Standard (AES) with a 256-bit key (AES-256)
- Supports the compliance of industry regulations
- Easily gets integrated with systems
- Should have an automatic key rotation and revocation system
- Must provide reliable security
- Scalable
Our AppleshineTech key management solutions consist of all the above-mentioned points. These systems make sure that your data is protected at all costs.
Conclusion
Key management is an important element in cryptography to maintain the security, confidentiality, and integrity of data. Especially for businesses and organizations, to protect their valuable data from cybercrimes is a critical task.
Using an effective key management system, you can protect your data from being breached and accessed by unauthorized users. Key management solution providers like AppleshineTech offer excellent security solutions to safeguard your data.
FAQs
1. What is key management in cryptography?
Key management in cryptography is the practice of securing the creation, storage, distribution, rotation, and destruction of encryption keys to protect data from cybercrimes
2. Why is key management important for security?
Key management is important for security because if the encryption keys are not kept safely, there is a high chance of a data breach.
3. How do key management systems protect data?
Key management systems protect data by storing the encryption keys in a well-protected place where only authorized users can access the information by decrypting it.
4. How can I improve my organization’s data security?
You can improve your organization’s data security by using a key management system to improve your data security through the use of encryption keys.
Also read:
Database Security: How It Protects Your Data and Works Hand-in-Hand with Data Encryption
The Role of HSMs in Securing Digital Payments and Financial Data
What Is Key Management? A Practical Guide to Securing Encryption Keys

